Cybersecurity & Guidance


Cybersecurity & Guidance
Cybersecurity is the top threat facing business and critical infrastructure in the United States, according to reports and testimony from the Director of National Intelligence, the Federal Bureau of Investigation and the Department of Homeland Security. All water systems should act to examine cybersecurity vulnerabilities and develop a cybersecurity risk management program.
Cybersecurity News
AWWA UPDATE: AWWA supports introduction of collaborative cybersecurity legislation
Legislation that supports AWWA’s recommendation for a collaborative approach to cybersecurity in the water sector was introduced in the U.S. House of Representatives. H.R. 2594 authorizes an independent, non-federal entity to lead the development of cybersecurity requirements in the sector.
AWWA’s Statement for the Record
AWWA submits Statement for the Record following Senate hearing on cybersecurity in the water sector
Water associations’ joint letter on cybersecurity
AWWA leads joint association letter to Congress on cybersecurity priorities
AWWA Cybersecurity Assessment Tool & Guidance
Are you a community water system or do you support community water systems? If so, federal legislation requires systems serving 3,300 or more persons to consider cybersecurity threats in your risk and resilience assessment, as well as in your emergency response plan. This may sound daunting, but AWWA is here to help systems of all sizes.
Planning Resources
AWWA has developed a set of resources to aid water utilities in building cyber-resilience. In combination they are designed to help a system identify potential exposure to cyber threats, set priorities, and implement a proactive cybersecurity risk management strategy. These also facilitate compliance with the cybersecurity provisions in SDWA §1433.
- START HERE: Water Sector Cybersecurity Risk Management Guidance. Practical, step-by-step guidance from AWWA focused on addressing vulnerabilities in the process control systems. Following this guidance saves time and yields more comprehensive, accurate and actionable recommendations from the Assessment Tool. The following templates are provided as supplements to the Assessment Tool:
- Assessment Tool. This interactive tool begins with a Getting Started Guide that seeks to ensure systems address a fundamental set of controls that eliminate common threats. The steps asks the user to follow the Small Systems Option, recommended for systems serving ≤ 10,000 persons, or the Full Assessment Option. Based on the systems response to questions regarding technology applications, the tool generates a customized, prioritized list of controls that are most applicable. Systems will use this output to assess the implementation status of critical controls designed to mitigate cybersecurity vulnerabilities. The output include a “due diligence” page and mapping to EPA’s priority cybersecurity controls list. AWWA website login is required for access.
About These Resources
AWWA’s Cybersecurity Guidance and Assessment Tool have been updated and revised to maintain alignment with the NIST Cybersecurity Framework (the key set of standards, methodologies, procedures, and processes designed to align policy, business, and technology solutions to cyber risks), and with Section 2013 of America’s Water Infrastructure Act of 2018 (AWIA).
Together, these resources constitute a voluntary approach for how a utility can implement applicable cyber controls from the NIST Cybersecurity Framework, and also fulfill the cybersecurity provision in AWIA §2013.
AWWA’s guidance and tools have been recognized by the U.S. EPA, Cybersecurity and Infrastructure Security Agency (CISA), NIST and several states for aiding water systems in evaluating cybersecurity risks.
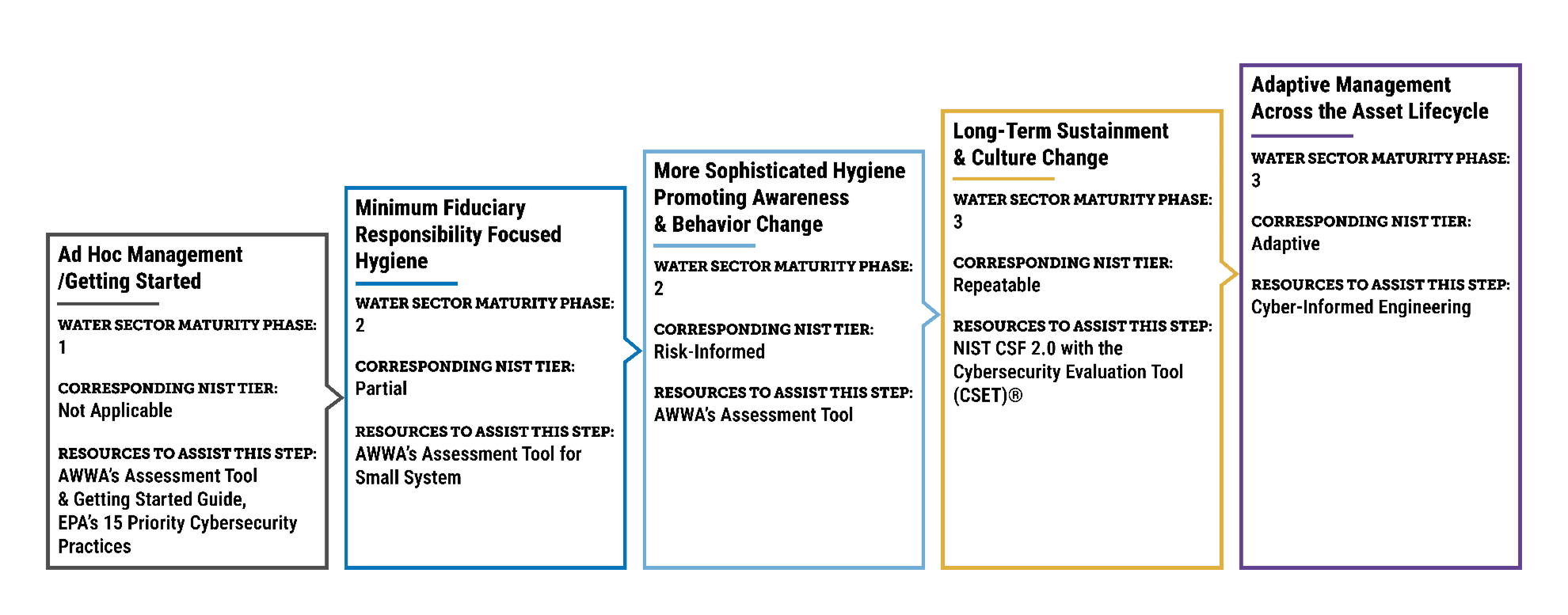
Growing your utility’s cybersecurity maturity. This figure shows the levels of cybersecurity maturity (adapted from SANS), and how AWWA cybersecurity resources fit within this model.
Cybersecurity: What Water Utility Leaders & Professionals Should Know
Cybersecurity is now a mission-critical function for water utilities. AWWA has developed a robust suite of guidance to help water utilities understand policies, comply with requirements and implement best practices.
To suggest updates and clarifications to this information, please email Kevin Morley, AWWA manager of federal relations, at kmorley@awwa.org.
Cybersecurity Oversight Options Explored
AWWA commissioned a report that explores industry-led regulatory options to support water sector cyber resilience, including the option of creating industry-wide cyber standards with oversight from a federal body, similar to what exists within the energy sector.
CISA Shields-Up Campaign
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) urges everyone to protect themselves online and adopt a heightened posture when it comes to security. CISA stands ready to help organizations prepare for, respond to, and mitigate the impact of cyber attacks.

Advertisement

Cybersecurity in the Water Sector Micro-learning
Water and wastewater systems have been targeted by cyber attacks across the United States. Utilities need to achieve cyber resilience to protect against growing threats and bad actors.
The micro-learning provides a high-level summary of the current state of cyber security, what utilities should expect and details of our Awareness-Analysis-Act Framework. The course also provides a directory of cybersecurity resources available from AWWA. These resources include manuals, standards, helpful links, tools, checklists, and longer eLearning courses.
Cybersecurity Micro-learning
External Resources
Beyond AWWA, many organizations and agencies have created helpful cybersecurity resources relevant to protecting water systems.
EPA – Cybersecurity Best Practices for the Water Sector
EPA – Water Sector Cybersecurity Brief for States
EPA – Cybersecurity Incident Action Checklist
EPA – Drinking Water or Wastewater Cybersecurity Risk Assessment Tool
EPA – Water Resilience Tabletop Exercises
EPA and the Bipartisan Infrastructure Law Fact Sheet
EPA – Cybersecurity Assessment and Technical Assistance and Assessment for Water and Wastewater Utilities
America’s Water Infrastructure Act: Risk Assessments and Emergency Response Plans
Baseline Information on Malevolent Acts for Community Water Systems
Small System Risk and Resilience Assessment Checklist
Drinking Water and Wastewater Resilience Resources
Cybersecurity: 2021 State of the Sector Industry Survey Report
15 Cybersecurity Fundamentals for Water and Wastewater Utilities
Report Incidents, Phishing, Malware, or Vulnerabilities
US-CERT Current Activity
Cybersecurity Evaluation Tool (CSET)
Implement Cybersecurity Measures Now to Protect Against Potential Critical Threats
Incident Response Guide: Water and Wastewater Systems (WWS) Sector
NIST Cybersecurity Framework
Critical Infrastructure Policy: Information Sharing and Disclosure Requirements After the Colonial Pipeline Attack

AWWA Policy Statements
AWWA’s policy statements are brief statements on protecting and improving water supply, water quality, management, and the interests of the public and the environment. They are written by consensus, subject to review and comment by AWWA committees, councils, and members. Because they represent AWWA’s position on these matters, they are approved by the AWWA Executive Committee of the board of directors.
- Strengthening the Cyber Resilience of America’s Water Systems: Industry-Led Regulatory Options
- AWWA Congressional Testimony – Mobilizing Our Cyber Defenses: Securing Critical Infrastructure Against Russian Cyber Threats
- Building Cybersecurity Resilience in the Water Sector
- What Does More Look Like (Journal AWWA)


Technical Committee Engagement
AWWA members are recognized globally for their industry expertise and their generosity in sharing that expertise for a better world through better water. AWWA members participate in committee activities, developing conference programs, writing technical manuals, developing standards, creating educational content and contributing to AWWA publications. Committee members primarily interact through conference calls, emails, and face to face meetings at conferences and events.
Inorganics Committee
Inorganic Contaminants Research Committee
Emerging Water Quality Issues Committee
Advertisement